Signal jamming
At present, the control of UAVs mostly uses radio communication technology. By transmitting high-power jamming signals to the target UAVs and suppressing the control signals, the UAVs can be forced to land or return by themselves.
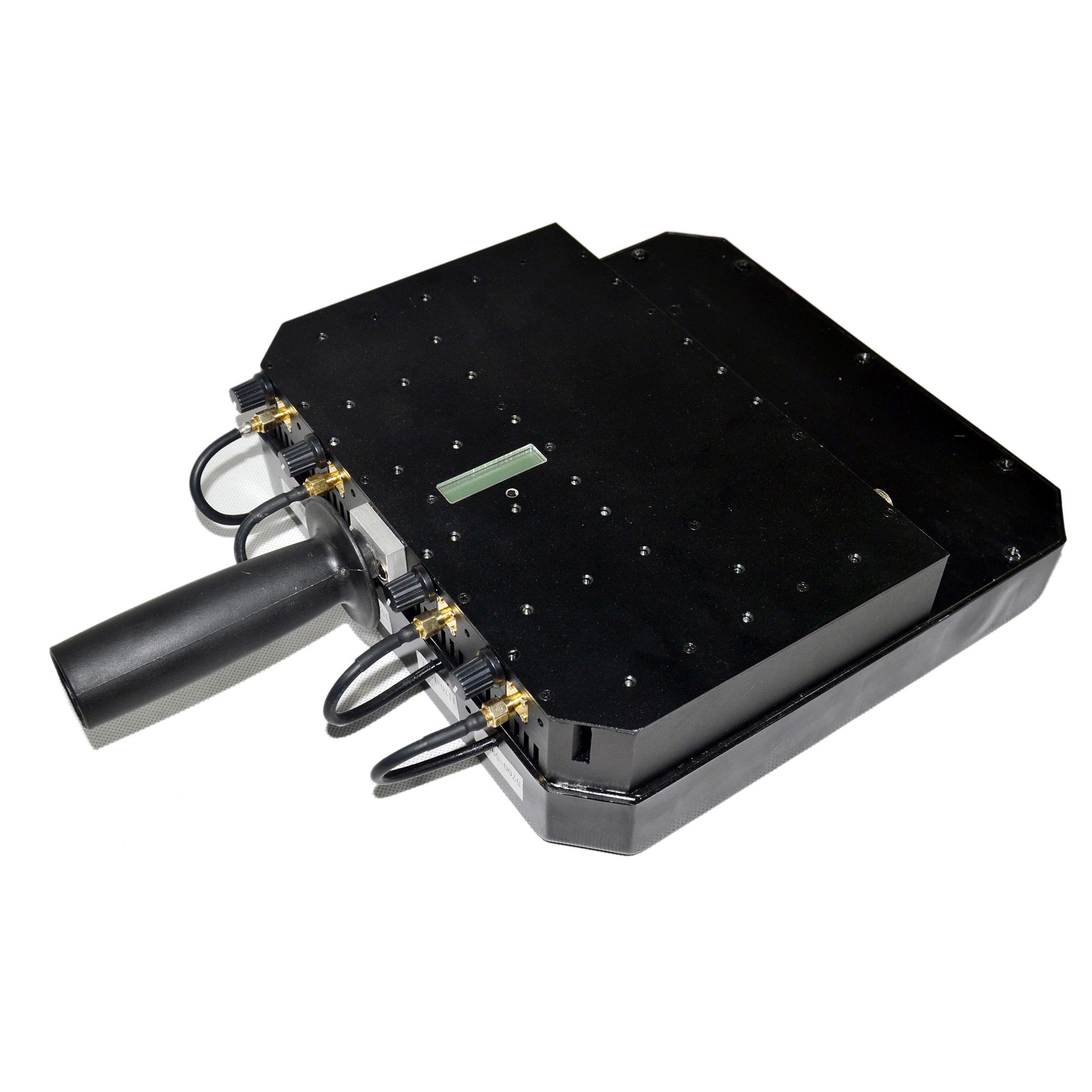
Jammer mart used this principle to develop a gun-shaped drone jammer. This gun installs an electronic jammer on the frame of the rifle. Once the trigger is pulled, the jammer will send a full-band jamming signal to the drone, so that the drone is out of the control of the operator and cannot receive the control signal. Automatically land on the ground.
Once the drone's signal is messed up, it usually has 3 options: fall to the ground, return to the operator, or descend smoothly. This rifle has an effective range of 500 to 2000 meters.
GPS spoofing
At present, under normal circumstances, most consumer drones will prefer GPS navigation for flight control, while civilian GPS signals are unencrypted, which leaves usable space.
The main principle of GPS spoofing is to send false geographic coordinates to the control system of the drone, thereby controlling the navigation system and inducing the drone to fly to the wrong place. The GPS signal can be generated by a generator, or it can be pre-recorded and then replayed. Since the GPS signal received by the drone is always based on the signal source with the strongest signal, as long as the artificial GPS signal on the ground is strong enough, it can cover the real GPS signal from space, thereby deceiving the drone. GPS receiver module.
At present, various countries have set up no-fly zones in core areas, and many drone manufacturers have set them in the built-in firmware of drones. In no-fly zone, the drone cannot take off, even if it reaches the no-fly zone. Automatic landing. So, as long as a man-made GPS signal on the ground simulates the geographic location as the coordinates of a no-fly zone, the drone can be forced to land on its own.
Radio hijacking
At present, most of the control signals used by drones are in conventional civilian frequency bands such as 1.2GHz, 2.4GHz, and 5.8GHz. With the rapid development of open-source hardware such as Arduino and Raspberry Pi and the popularity of software-defined radio (SDR) technology, ordinary enthusiasts It is also possible to use the hardware purchased from the Internet and the software source code obtained from the forum to simulate the remote control to send control signals to the drone and overwrite the signal of the real remote control, so as to obtain the control of the drone.

Hacking
Many drones directly use Wi-Fi to interact with mobile devices such as mobile phones and tablets for the convenience of users. In this way, some hacking techniques that are already mature on the Internet can be directly applied to drones.
For example, through the open port in the UAV control system or password guessing and other means, enter the control system to realize the control of the UAV. The legendary hacker Samy Kamkar, who developed the "Sami worm", used this principle to write a drone hijacking software called "SkyJack" and installed the software to
In a specially configured drone, SkyJack flies through the air and looks for other drones within Wi-Fi range, then hacks into that drone and takes control.
Professionals engaged in anti-drone jammer applications in the industry said that the current domestic anti-drone technology is still in the exploratory stage. Radio hijacking technology is difficult to achieve due to the encryption of radio signals by various drone manufacturers, and hacking technology due to The threshold is high and it is not easy to commercialize, so the currently used technology is mainly based on interference blocking.